Thanksgiving turkey may symbolize the holiday for most people, but messaging security firm Proofpoint is warning businesses to watch for a whole flock of cyber security threats that peak around Thanksgiving.
In preparation for the rise in phishing scams expected over the weekend, Proofpoint is urging businesses to take particular care with email and social media scams.
Scary Cyber Monday
While email phishing and spam are well-known channels for these campaigns, social media channels give crooks a new set of tools to reach their potential victims.
Because many of the defenses that organizations have deployed to stop unsolicited email are not effective against social media spam and phish, they are able reach end-users when email-based campaigns would have been blocked, Proofpoint noted in a blog post.
The company cites the example of a typical scam like the fake “Amazon Gift Card” promo Facebook Page that takes advantage of Black Friday and Cyber Monday shopping:
This gift card multi-variant phishing campaign used realistic-looking branding and creative to entice potential victims to click. As in the email-based phishing campaigns, the lures in social media spam use stolen branding for major retailers -- in this case Amazon -- to attract potential victims to their scams. In this regard, the retailers whose branding and creative are stolen are also victims, much like in malvertising based on poisoned ad networks,”
For any retailer investing in Cyber Monday, accounts like these steal visitors, siphon sales, damage the brand and hurt customers who fall victim to their scams.
Email Breaches
This comes in the same week that Heimdal Security estimated that more than 6 million e-mail accounts have been compromised in the past three months.
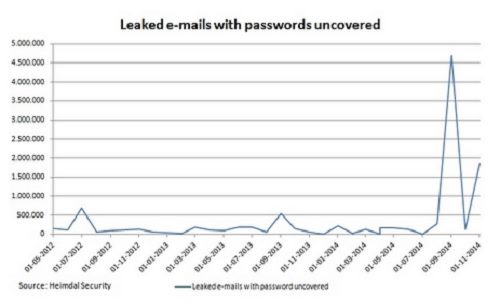
According to Heimdal, its intelligence team analyzed the e-crime market statistics for the past few months and concluded that the problem is probably much worse than the 6 million. That figure is only for analysis of a small time slot this year, which has seen a number of significant security breaches since January.
Into the Wild
In a blog announcing the figures, Aurelian Neagu says that the breaches have left millions of email credentials from corporate logins and private consumer email accounts out in the wild.
If we analyze the statistics, we have to admit that the 6 million accounts which have been stolen, they simply represent only the tip of the iceberg and the problem is much larger. As a security company, it’s our job to emphasize this number only covers the last 3 months. The actual number could be more than 20 times higher,” he wrote.
He added that of the email accounts that Heimdal checks, they have managed to crack on average about 4 percent of the passwords, although that is running at 6 percent in recent weeks.
If that figure is extrapolated into the business sector then in an enterprise with, for example, one thousand employees, this means that the details of 60 of them have been leaked outside the enterprise, a figure that is far too high for anyone’s peace of mind.
However, Neagu says that this is not a problem that is exclusive to email and that it reflects a pretty scary year in respect of data breaches in general.
Intensified Attacks
In fact, the most recent Trend Micro’s security roundup for the first half of this year shows that the severity of these attacks have intensified, especially against financial, banking institutions and retail outlets.
It also showed that more than 10 million personal records have already been exposed as of July 15, with the majority of breaches occurring in the business sector.
These incident attacks in the second quarter affected consumer's personal information as well as the theft of data such as customer names, passwords, email addresses, home addresses, phone numbers and dates of birth.
By the end of July, 400 data breach incidents were reported, High-risk vulnerabilities affected various components of Internet browsing and Web services, including server-side libraries, OSs, mobile apps and browsers.
Title image by Joop Snijder Photography / Shutterstock
