Everyone that uses the web knows that it's a wild, wild world out in hyperspace. But there’s other places that are equally wild, and positively dangerous for your data -- and most of them are in your enterprise. A recent white paper by Quest outlines three of the major problems, and six simple solutions to solving the problem of data governance.
Data in the Enterprise
Over recent months, there have been numerous papers and even conferences on the business value of your content and how information is no longer just a byproduct of business, but also a business goal in itself.
By that we mean that your enterprise is only as good as the content and data it contains and the better it is managed the better your business will be. In respect of the many people who have made interesting contributions on it recently, we can cite Brendan Coveney, GM for the Americas at the Nuxeo annual meeting, while Gartner, Forrester and earlier on in the year the AIIM State of the Industry report all indicate that companies are starting to realize the intrinsic value of business content.
That’s all very good; the way it should be. But the higher the value of the content, the greater the target it becomes for hackers and other nasties, who are looking to exploit that value for themselves.
There is hardly a week goes by without a report of some company succumbing to data breaches by outside third parties, or even by people on the inside of your enterprise.
Unfortunately, in this case, the quaint medieval custom of burning these ne’er-do-wells at the village crossroads is gone, and the only protection now is effective and efficient information management and governance.
The starting point for that is identifying where the likely weaknesses in your information fortress are, and how to shore those weaknesses up. Quest has been looking at this in some detail and has identified three areas that are the most commonly identified weak points across numerous enterprises.
The first thing that needs to be said that is that Gartner in its Security and Risk Management Lessons from March of this year argues that data access decisions should be based on an assessment of the risks and benefits of a given level of data sharing, as well as an assessment of the process, people and technology that can securely enable that sharing.
In concrete terms, Quest, it its paper Data Access Governance breaks this up into three areas:
1. Inefficiency
Securing and controlling access to data is a very time-consuming process. Currently, for most companies that are even aware that their data access protocols are an issue, actual practices in securing that are inefficient, whether you are manually securing unstructured data, or whether it is data that is being dealt with automatically.
To secure it properly, enterprises need to assess where in the environment your data resides, assess how much data loss there is from the use of file servers and NAS devices, and even develop an inventory of what’s available in your SharePoint deployments. All very time consuming, you’ll no doubt agree.
2. Ineffectiveness
After answering the question as to who has access to your data, the next big question is whether they should have a given level of access or not. Does IT know what level of access should be offered to employees, and should this decision be left in the hands of the IT department at all?
The chances are that they shouldn’t be allowed decide, as this is ultimately a business decision. But, as in the case of most companies, there is no clear policy on who makes the decisions. Chances are in this situation there’s also going to be a lot of unstructured and orphaned data lying around with no one to take responsibly for it.
3. Lack of Agility
In an ideal world we all use predictive analytics and we all know about problem coming down the road before they happen. But the reality is different and most companies are reactive -- they react to problems as they appear. However, if you only react to a problem as it happens, it is very difficult to be agile, and we have seen before that agile companies are winning companies.
For example, if data is assigned to a particular employee and that employee leaves, what then? If your company takes over another company, where does that data go and who takes ownership of it?
There are many different solutions from many different vendors that address these issues, like software for access governance, data discovery, automation and access control.
However, like other areas of enterprise content management, the key to all of this is in planning and policy development and there are six steps you can take to fix that immediately:
Six Steps to Data Governance
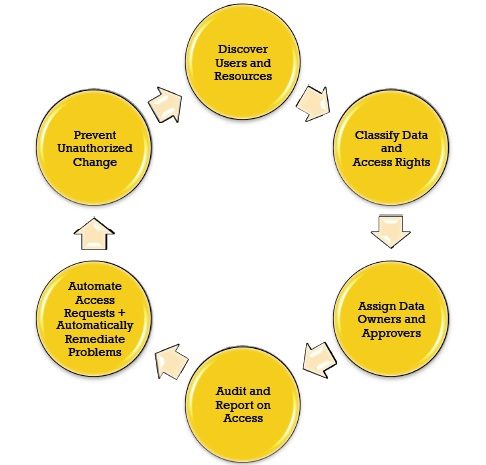
6 steps to data governance
1. Discover Users and Resources
The first thing that needs to be done is to develop a complete inventory of your infrastructure, which will include a full list of users and resources, as well as identifying any unstructured or orphaned data that exists in the infrastructure. With SharePoint use now as widespread as it is, you will have to discover and document the extent of its use, what’s in it, and who has access to it.
2. Classify Data and Access
Once that is completed you will have to identify what kind of data you have. By this we mean whether it’s confidential, whether it's data that needs to be kept for regulatory reasons, whether it is data that is actually being used, or whether it should be shunted off into a (identified) corner of your records management system. In the event that there is no records management system, it should be moved at least to somewhere it is not causing a fuss and costing money to store.
3. Assign Data Owners and Approvers
Following that comes the step which really starts to show dividends. Data needs to be assigned owners, which should be decided on status, need, location or other business values rather than technology values. This is a role for the business owner. During this phase, compliance checks need to be implemented, so, for example, that the data requester can’t also be the approver. This should also be where automated workflows for request processing are implemented.
4. Audit and Report on Access
As data is constantly being updated and changed according to business needs, a review of access procedures needs to be implemented on a regular basis to see if access permissions need to be changed. This will also enable the enterprise to identify data access issues that are not working and to change processes according to needs.
5. Automate Access Requests
For security reasons, access to data should only be assigned according to roles within the organization. There are many ways of doing this, but Quest suggests a request portal where users can request access, and where those requests can be reviewed by appropriate personnel. It is also advisable to implement automated responses to requests so no deviations occurs in responses.
6. Prevent Unauthorized Change
Finally, there are always data groups and areas that need to be secured and they need to be secured from ever being changed. These should be locked-down with alerts in place that notify if any changes or attempted changes are made. A log should also be created of all changes that have been made -- a log that is also secured in its own right.
Final Thoughts
The objective here is to achieve full visibility of data in your system that will include a view of what you have, who has access, and even where its being used and where it’s going.
While there are probably other points that should be considered for individual circumstances, generally speaking these are the main ones, which can be summed up by underlining the role of planning in anything and everything to do with data.
